Since the internet's early days, scammers have been working to steal our money and sometimes our identity. And while we as internet users have become more aware and are more capable of identifying scams, the bad guys have gotten better too, which means danger is still lurking behind every digital corner.
However, the best defense against cybercrime is not to avoid using the internet. Doing that would be denying ourselves all the best things the internet offers, such as educational resources, social media, and pictures of cute dogs. Instead, the best thing you can do is to inform yourself about how hackers work and about the most common types of scams out there.
Email scams, also known as phishing, are some of the most prevalent threats, so it's essential to understand what they are and what they look like so that you can steer clear and stay safe while surfing the web. Read on to find everything you need to know.
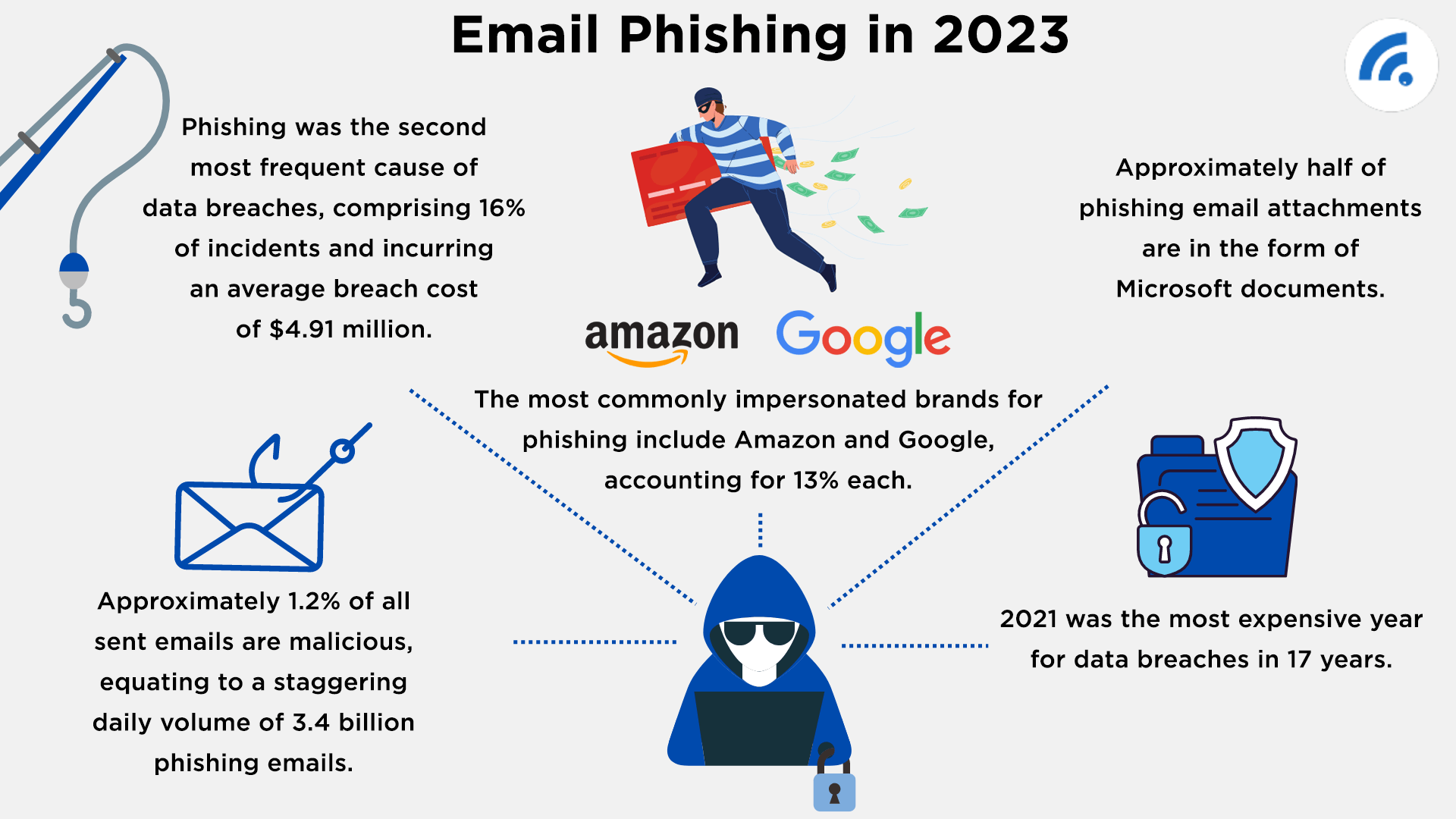
Understand the Risk of Email Phishing
To help you understand the risk that email phishing poses, consider the following:
What is Phishing?
According to phishing.com, phishing is a type of cybercrime in which hackers contact you while posing as a legitimate institution or organization to get you to provide sensitive or private information. Once they have this information, they most often use it to commit financial or identity theft, the consequences of which can be extremely severe.
This type of phishing can occur over the telephone, via SMS, text message, or, as is most often the case, through email.
Other phishing attempts will ask you to download a file or click a link, and doing so will infect your computer with malicious software that can cause your personal information to end up in the wrong hands.
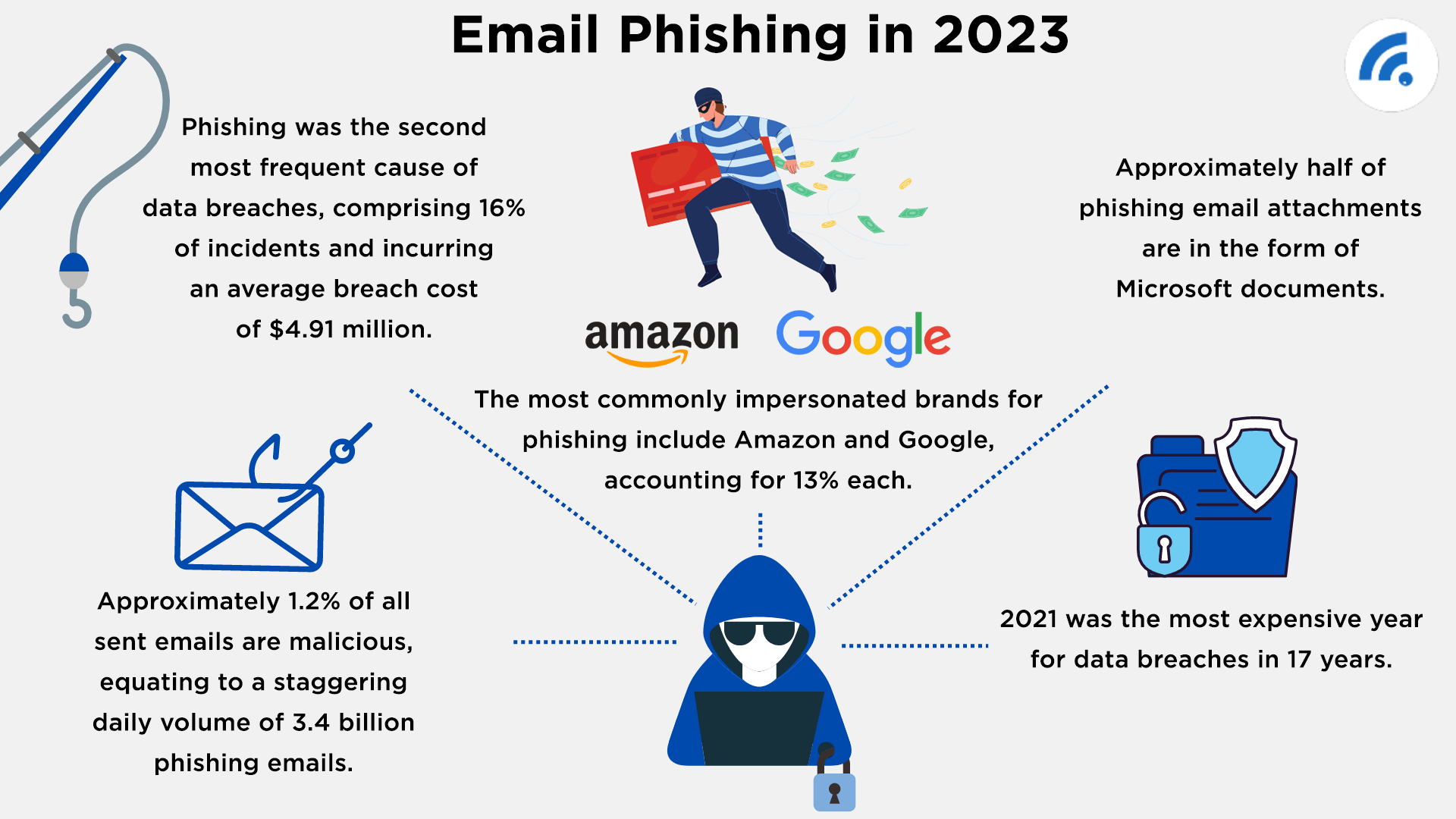
Spoofing
Integral to almost all phishing attempts is a website or email spoofing. This is the practice of creating a website or email template that nearly perfectly mimics a legitimate website. These designs are very professionally done and can be almost impossible to distinguish from the real thing.
Often, the website design will be very similar, but the URL will be slightly off, as is the case in this example of a spoofed version of Amazon:
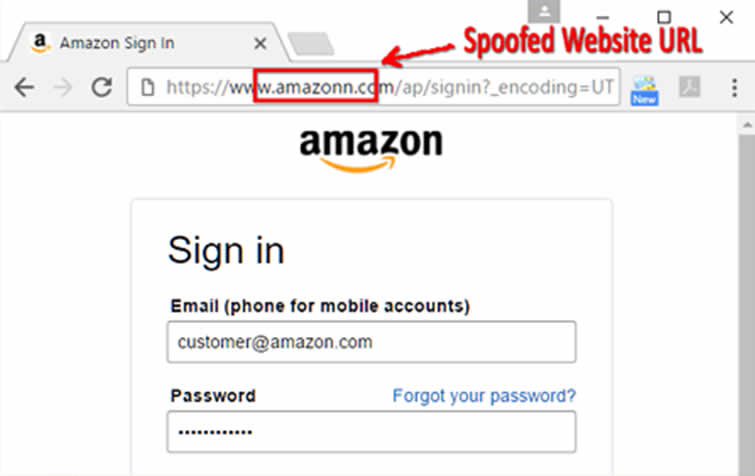
When it comes to email, spoofed emails make it incredibly difficult to know if the email is real or not, which is why you need to know what the most common scams are and how to spot them. Here are a few examples of spoofed emails, one from "Netflix" and the other from "Bank of America."
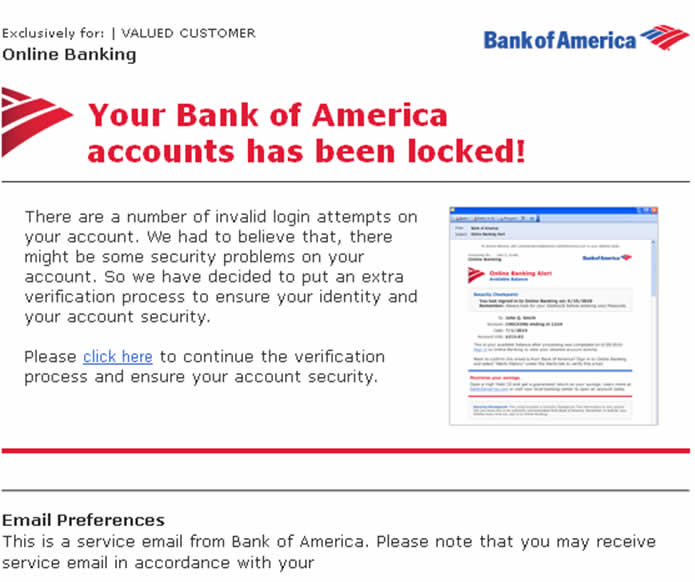
Even to a trained eye, these appear to be 100 percent real, even though there are always slight differences that will tip you off to the scam. But not recognizing these differences means falling for these spoofed emails and succumbing to the consequences that can result.
9 Most Common Email/Phishing Scams
There are countless examples of email phishing, so many that we could never identify all of them for you. However, we can point out some of the most common, as well as some of their characteristics, so that you can get better at spotting them and knowing when not to click.
Here are the nine most common:
Government Emails
Who is more trustworthy than the federal government? Well... maybe that's not the best question. But regardless of your politics, we still tend to think of the government as a safe space, one that can't be hacked. Yet this is simply wrong. Emails are designed to look like they are from a government agency, most often the FBI or Medicare, and they are designed to trick you into giving away your personal information.
These phishing emails are exceptionally dangerous because they often ask for your most important information, such as your social security number, and because the email appears to come from the government, we are more likely to give this information away.
Common scams include telling you that you have been investigated for "downloading illegal files" or that you need to update a government account with your correct information. However, when the government requires you to do something important, they typically send you a letter in the mail. If you've signed up for paperless communications, check to ensure the suspicious email is coming from the same sender as previous messages. You can also contact the agency directly to verify if your email is real.
Fake Tax Emails
Similarly, hackers will prey upon people's fear of making a mistake on their taxes to get your personal information and rob you. These emails are much more common around tax time (early Spring), and they usually say one of two things: you're being audited and need to submit information, or you've been pre-approved for an early refund.
The early refund ploy is a classic example of something being too good to be true, so be skeptical if you receive a message of this nature. And if you're being audited, the IRS will communicate with you in some other way besides a quick email.
Getting audited is a huge deal, so if you get a message saying this is about to happen, you should first get in touch with the IRS. If it's real, they will most definitely know about it, and if it's fake, this will save you the trouble that comes with falling for a phishing attack.
Help me!
This particular scam is troubling because it plays on our natural desire to help other people. These emails will come from someone claiming to be in a desperate situation that needs your help. Sometimes they come from strangers, but others are sent by people you know whose account has been hacked. Yet no matter what, they will ask you for one thing: money.
Sometimes they will directly request you wire them some money, but in other cases, they will ask you to book them a hotel room or buy them a plane ticket. They will typically tell you some sob story about how they had been robbed or how they lost their wallet and now have no money to return home to safety. They may ask you to send them your credit card information, or they may send you a link to click on. Either way, don't do it.
If the email comes from someone you know, there's a simple solution: contact that person to find out if they really are in danger. When the email comes from a stranger, it's phishing. Ignore it. It's as simple as that.
Update Your Account
Another common phishing scam comes in the form of a spoofed email from a trusted organization, saying there is a problem with your account that you need to fix immediately. To make this "easier" for you, the email will usually come with a convenient link to a spoofed website where you will provide login information for that site. But, since everything is fake, all this will do is give your private information to the hackers, which they will use to steal whatever they can from you.
To prevent this, remember that if there is a problem with your account, whichever company you are working with will probably not try to reach you by email. If they do, they will usually refer to you by name, and there will typically be several layers of security that you must pass through before you can actually make changes.
For example, you may need to enter a code sent to your email or cell phone, or you will need to answer some security questions. They will never send you a link that brings you immediately to your account.
Should you get an email like this and you really can't tell if it's real, the best thing you can do is reach out to the company or institution that contacted you to see if there is a problem. If there isn't, this is a great chance for you to alert them that they have been attacked and need to address the security of their site.
You're a Winner!
We all dream of winning the lottery, and while it's quite unlikely this will happen, it's impossible if you don't first enter the lottery. This is where we get the whole "you've got to play to win" idea.
However, email scammers will play on our desire to win things and send fake emails claiming you've won a special prize. These prizes can range from free vacations to iPhones to large amounts of cash. But to claim this prize, you must provide the person who sent you the email with some personal information, which should be a giant red flag.
These scams are tempting - we all love the idea of free stuff - but before you turn over your private information to a stranger, ask yourself: did I enter this lottery or contest? If the answer is no, this email is undoubtedly a scam. If you're unsure, look through your emails to see if you have any records of entering. Another option is to try and find out who is making this offer so that you can contact them directly. Not being able to find this contact information is another red flag, and it's always better to be safe than sorry.
Extortion
Often referred to as "sextortion," this scam usually comes in the form of an email from an anonymous sender saying that they have figured something out about you that could be compromising. For example, they may say that they have caught you watching pornography or claim to have photos of you that you wouldn't want to be released to the public.
Often these hackers get your information from accounts that have been deactivated or deleted, which can cause them to know some things about you that will make anyone uneasy. But all this does is make the scam seem more real, even though it's not. Sometimes they will send the information using a spoofed email that looks like it comes from somewhere official, but this is only meant to make their false claim more believable.
However, no matter what the sender claims to have, they will almost always ask for some "confidentiality fee," which they will almost always ask you to pay in Bitcoin or some other cryptocurrency that can't be traced.
For those who don't engage in this potentially risky behavior, avoiding this scam is easy because it's impossible for the sender to have something that doesn't exist. However, if you're worried there might be some stuff about you that you don't want to get out, it's still not worth paying. You'll never get that money back, and there's a good chance there was never any real danger in the first place.
Cloud Files
The cloud has made life considerably easier for most of us, and scammers know this, so they often use file-sharing services to access your personal information. Typically, to execute this scam, hackers will send you a spoofed email that appears to come from Google Drive, Dropbox (one of the most commonly spoofed websites), Office 365, etc., informing you that someone has shared a document with you.
These emails will usually appear to come from someone you know, which means they will look genuine at first glance. If you click on the link, you will be brought to a login page - again, not suspicious - but filling out your information will provide the hackers with access to your accounts, which they will then use to access other accounts and steal your identity.
To prevent this, the best thing to do is double-check the sender's address to make sure you recognize it. If it looks wrong, it probably is. Should the email come from someone you know, and it seems suspicious, double check with that person before opening the document. Remember, when in doubt, don't click.
Package Delivery
Ordering things online has become a part of life, so much so that we often forget we've ordered stuff until it arrives at our front door. Or, people send us stuff without us knowing about it. Either way, this represents an excellent opportunity for hackers to try and steal your information.
In most cases, the email will be a spoof made to look like it comes from UPS, FedEx, DHL, the USPS, or some other delivery service. It will tell you that there is a problem with a package on the way and that you need to provide some more information to complete the delivery.
Conveniently, there will be a link for you to click on that will ask you to provide login information, but because the site is false, all you will be doing is providing your personal information to a hacker. In some cases, clicking on the link will trigger an automatic malware download, which can wreak havoc on your computer and ruin your life.
Preventing these scams requires you to know how to spot spoofed emails and websites. If you're unsure if the email is actual or not, look back into your email history to find an email you previously received from this company and compare it to the one that looks fake. If there is not the same, then there's a problem, and you should contact the company directly to find out what is happening. Spoofed websites will often include misspelled names or weird punctuation, so keep an eye out for this if you click on the link provided in the email.
Check This Out
Email forwarding is nowhere near as popular as it used to be, but it's still hard for us to resist an email that says something like "check this out!" And it's even harder to ignore these when they come from someone we know, which is why this scam works so well.
In this version of phishing, hackers send you an email that looks like it comes from someone you know. The name will be the same, but the email address will be slightly different, which is how you know it is a scam. In the body of the email, there will usually be a link to a photo or website that you're supposed to check out, but clicking on it will start a download on your computer that could cause you some serious problems.
If you get an email from someone sharing something, make sure to double and triple-check the address. Look back for past emails from that person, and if you can't find one, ask yourself why this friend has chosen now to send you an email. To be safe, send them a message on another platform to find out if it was really them that sent that email, and if it wasn't, this would alert them that someone hacked their email and that they need to address the security of their account.
How to Stay Safe From Email/Phishing Scams
The best way to stay safe from phishing scams is to know what they look like. The nine we've outlined above are the most common, but there are always new ones being circulated. As a result, to stay safe from phishing scams, keep the following tips in mind:
- When in doubt, don't click.
- Always assume that something that seems too good to be true is too good to be true.
- Double check the sender's addresses and URLs. Spoofed emails and websites are usually only slightly different and require you to pay close attention.
- Seek out alternative information, either from the company that is supposedly contacting you or on Google, to see if other people are receiving similar emails and if they are legitimate.
- Contact friends and family when you receive a suspicious email from them to see if it's real or not.
- Look for spelling errors in the messages you receive. Real companies spend time ensuring the emails they send are correct, and hackers don't.
- Check to see if the company addresses you by name. This doesn't necessarily mean the email is legit, but it's a good sign.
To give yourself the best chance at staying safe while using email, it's essential to know how to recognize fake emails from real ones. Not sure if you're up to the task? Take Google's phishing quiz to see how good you are and to learn some of the best ways to prevent falling for phishing attempts.
What to Do if You Click
If you do happen to click on something and realize you've fallen for a phishing attack, here's what you should do:
- Contact your bank to let them know what happened. Depending on the nature of the attack, it may be wise to cancel your cards and reissue them.
- Contact the authorities so that they are aware of this type of attack and also so that you can prove it happened in the event your identity is stolen.
- If the phishing attack came from a spoofed email or website, contact the company or institution to alert them that someone is using their graphics and email lists to steal from people.
- Contact credit reporting agencies to let them know of potential fraud.
- Monitor bank and credit card accounts to ensure no suspicious activity.
- Consider scanning your computer for malicious software or resetting your computer to a point before the attack. If you're not comfortable doing this on your own, take your device to a professional to have it inspected.
Hopefully, you won't need to follow any of these steps. But if you even slightly suspect something is wrong, take action to prevent yourself from getting into real trouble down the road.
Conclusion
Nowadays, most email clients, especially Gmail, are quite effective at filtering out scam attempts and keeping you safe. But they are far from perfect, which means bad emails are bound to get through, and hackers are constantly improving, meaning it is likely no end in sight.
As a result, the only thing we can do to stay safe is to remain vigilant, and now that you know what some of the most common scams are, we hope you can email your way into the future without fear.