Online privacy is not about becoming invisible. For most people, it is about control: who can collect your data, what they can do with it, and how easily you can say “no.”
This guide breaks digital privacy down into practical steps. You’ll learn what puts your information at risk, what Google can see (and how to change it), how data brokers work, and what to do today to bolster your online privacy.
Key Takeaways: Protecting Your Personal Info Online
- Most Americans are concerned about how companies use their data (81%), and many are also concerned about government data use (71%).
- A lot of people click “agree” without reading privacy policies (56%), which is why simple privacy habits matter.
- Data breaches are still happening at huge scale. The ITRC tracked 3,158 U.S. compromises in 2024, and reported 1.35 billion victim notices. (IRTC, Jan 2025)
- The financial impact of breaches is big, too. IBM reports an average cost of $4.44M globally, and $10.22M in the U.S. (IBM, 2025)
- Google gives you tools to review, delete, and auto-delete some activity (including options like 3, 18, or 36 months).
- California’s new DROP tool lets residents send one delete request to 500+ registered data brokers, with brokers required to begin processing requests starting August 1, 2026.
What Is Digital Privacy?
Digital privacy is your ability to decide how your personal information is collected, shared, and used when you are online. It's the right to decide which companies, apps, and platforms can track your behavior and store details about your life.
Personal data can include:
- Identifiers (name, email, phone number)
- Location signals (precise location, “near me” searches, check-ins)
- Device information (IP address, device IDs, browser settings)
- Behavior (searches, clicks, watch history, purchases)
- Inferences (interests, demographics, “likely to buy” categories)
Privacy and security overlap, but they are not the same:
- Privacy is about control and limits on collection and sharing.
- Security is about protecting data from unauthorized access (like hacking or leaks).
Why Does Digital Privacy Matter In 2026?
Digital privacy matters because your data can be used in ways that affect your time, money, safety, and peace of mind.
People are worried, and many feel stuck
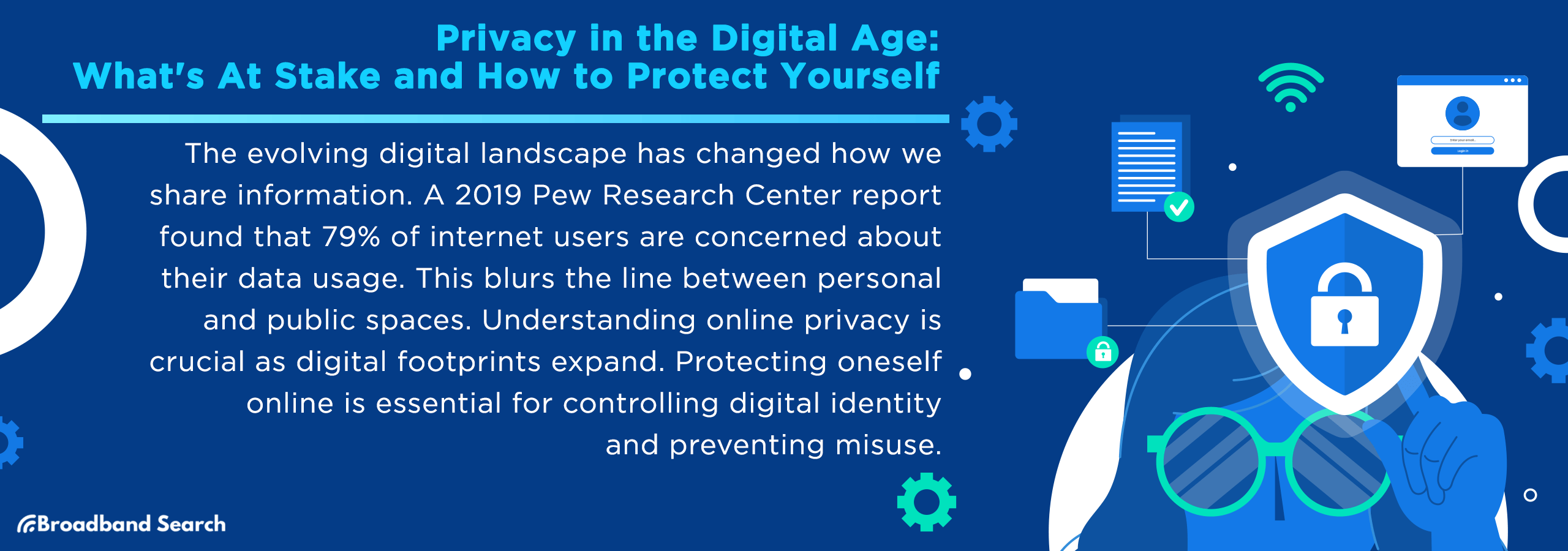
Pew Research found widespread concern about data use, and plenty of skepticism about how well privacy policies protect anyone.
If you have ever accepted a privacy policy just to get to the app, you are not alone. Pew reports that 56% say they often click “agree” without reading what they are agreeing to.
Breaches are still near record levels
The Identity Theft Resource Center reported 3,158 publicly reported U.S. data compromises in 2024, and 1.35 billion victim notices. Even if you do everything right, your information can still be exposed. (IRTC, Jan 2025)
The stakes are real
IBM’s 2025 reporting puts the global average cost of a breach at $4.44M, and the U.S. average at $10.22M. That’s per breach.
You’re not directly paying that, but you probably feel the fallout through fraud, account takeovers, and endless password resets.
What Are the Biggest Digital Privacy Risks Today?
Privacy risks range from leaked password and credit card information, to web trackers, to the smart thermostat in your home. Anything that is connected to the internet and has an account associated to your personal information is a risk.
Understanding the risks can raise your awareness of them and how best to protect yourself and your information. Here are the most common risks and how they can affect you.
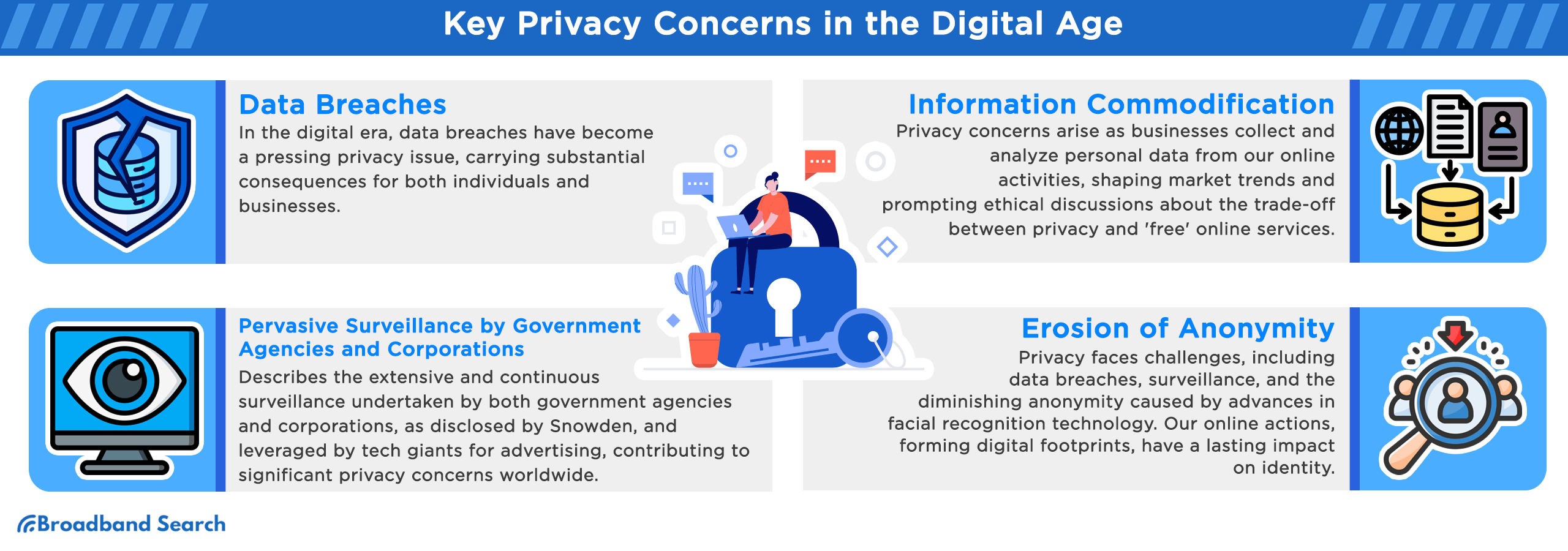
Data breaches and leaked passwords
When companies are breached, the data can include emails, passwords, addresses, Social Security numbers, credit card info, and more. The ITRC tracks breaches annually and shows the problem is not going away. Once your credentials are leaked, they often end up on dark web marketplaces where criminals buy and sell them.
Tracking across websites and apps
Every time you visit a website, cookies, tracking pixels, and browser fingerprinting technologies can follow you as you browse the internet. Advertisers use this data to build profiles and serve targeted ads. Most browsers (Firefox, Safari, and Edge) have third-party tracking turned off as a default, but you must disable it in Chrome. Fingerprinting, which identifies you based on your device's unique characteristics, continues regardless of cookie settings.
Data brokers and people-search sites
Data brokers collect information from public records, online activity, and purchasing behavior, then package and sell it to advertisers, employers, insurers, and others. People-search sites display your name, address, phone number, age, and relatives for anyone to see. Opting out is possible but time-consuming because their opt-out pages are buried deep in their sites. You may have to submit requests individually. California's Delete Act (also called DROP) creates a one-stop opt-out system.
Over-permissioned apps and “always on” devices
Many mobile apps request access to your location, contacts, photos, microphone, and camera even when they’re not needed to function. Apps can track your precise location in the background, building a detailed picture of where you go, when, and how often. Get in the habit of reviewing app permissions and revoking access to anything that isn't necessary.
AI and Smart Devices
Smart speakers, home assistants, connected cameras, and AI-powered apps often operate with always-on data collection. Voice assistants can accidentally record conversations. AI tools process your prompts and may store or use them to train models. Review privacy settings for every connected device and disable the features you don't need or want.
Common Privacy Risks and Quick Fixes
| Risk | What It Means | Quick Fix |
|---|---|---|
| Weak passwords | Easy for hackers to guess or crack | Switch to passkeys or use a password manager with strong, unique passwords |
| Third-party tracking | Advertisers follow you across websites | Enable tracking protection in your browser settings |
| Data broker listings | Your personal info is sold to third parties | Submit opt-out requests to major brokers like Spokeo, Whitepages, BeenVerified |
| Excessive app permissions | Apps access more data than they need | Review and revoke unnecessary permissions in phone settings |
| Old accounts | Forgotten accounts leak data in breaches | Delete unused accounts and enable breach alerts |
| Public Wi-Fi | Unencrypted networks expose your activity | Use a VPN or avoid sensitive transactions on public networks |
| Location tracking | Apps monitor where you go 24/7 | Set location access to "while using" or "never" for most apps |
| Smart device recordings | Always-on microphones and cameras | Disable recording features or mute devices when not in use |
What Does Google Know About You, And How Do You Control It?
Google services are deeply integrated into many people’s lives, from search and Gmail to YouTube and Maps. That adds up to significant data collection all about you. The good news is that it also provides tools to review and manage a lot of that data. Here's what Google tracks and how to manage it.
What Google Can Collect
Depending on what you use, Google can collect:
- Search activity
- YouTube watch history
- Location-related history (like Maps Timeline)
- Ads interactions and ad personalization signals
- Device and app activity connected to your account
Where to Review Your Google Activity
In your Google account, My Activity is the central hub for reviewing and managing activity.
In My Activity, you can:
- Filter by date and product
- Search for specific items
- Delete individual records or time ranges
How to Delete It (And Set Auto-Delete)
You can manually delete activity, and you can also set up auto-delete. You can set auto-delete to remove items that are older than 3, 18, or 36 months, depending on data type and setting area. Setting auto-delete is smart for ongoing privacy because it reduces how much Google stores and you never have to remember to delete manually.
Results About You: Find and Remove Personal Info from Search
Google’s “Results about you” tool helps you:
- Get notified if your contact info appears in Search results
- Request removal of results you would rather keep private
To set it up, go to your Google account settings and find "Results about you." Add your name, address, phone number, and email address.
A Gmail Ads Myth Worth Clearing Up
Google does not scan or read the content of your Gmail messages to show you personalized ads. Ads in Gmail are based on your activity in other Google services, not the text of your emails. Google does scan emails automatically for security purposes like spam filtering and malware detection.
How to Export Your Google Data
You can download a copy of everything Google has stored about you at Google Takeout. There, you can select the services you want to export (Gmail, Drive, Photos, etc.), choose your file format and delivery method, and click "Create export." Google will email you a download link when your archive is ready. This is useful for backups or for reviewing exactly what Google has collected.
What Incognito Mode Does (and Doesn't Do)
Chrome's Incognito mode and private browsing in other browsers prevent your browsing history from being saved on your device. They also clear cookies when you close the window.
Incognito does not make you anonymous online.
While in Incognito mode, your internet provider, employer, school, and the websites you visit can still see your activity. Google can still collect data if you're signed into your account. For better privacy, adjust your account settings, use tracking protection features in your browser, and consider a VPN or privacy-focused browser extensions.
The Quickest Ways to Improve Digital Privacy Today
If you only have 15 minutes, these actions are the easiest ways to improve your digital privacy quickly.
- Turn on passkeys where available. Passkeys replace passwords with biometric or device-based authentication and are far more resistant to phishing.
- Enable multi-factor authentication (MFA) everywhere. Use an authenticator app or hardware key instead of SMS codes, which can be intercepted.
- Reduce tracking in your browser. Enable Enhanced Tracking Protection in Firefox, Tracking Prevention in Safari, or third-party extensions like uBlock Origin or Privacy Badger in Chrome.
- Lock down phone permissions. Go to your phone's settings and revoke access to location, camera, microphone, and contacts for apps that don't need them.
- Start data broker removals. Submit opt-out requests to the biggest brokers like Spokeo, Whitepages, and BeenVerified. Mark your calendar to repeat every six months because removing information doesn’t prevent it from being repopulated.
- Audit Google activity controls. Visit myactivity.google.com, turn on auto-delete for 3 or 18 months, and review what's been collected.
- Use unique passwords. Install a password manager like Bitwarden, 1Password, or Dashlane and replace reused passwords with strong, unique ones.
- Delete old accounts. Use a service like JustDeleteMe to find and close accounts you no longer use.
- Turn off ad personalization. In Google, Facebook, and other platforms, disable personalized ads in your privacy settings.
- Review app subscriptions and permissions. Check your phone for apps you haven't used in months and delete them. They may still be collecting data in the background.
Step by Step: How to Protect Your Online Privacy
Privacy isn't one action. It's a series of small, repeatable habits. Follow these steps in order to build a strong foundation.
Step 1: Lock Down Your Logins
- Start by securing your most important accounts: email, banking, social media, and password manager.
- Enable passkeys if the service supports them. Passkeys use biometrics or your device's security chip to log you in, making phishing almost impossible.
- If passkeys aren't available, turn on multi-factor authentication using an authenticator app like Authy, Google Authenticator, or Microsoft Authenticator.
- Avoid SMS-based codes when possible because they can be intercepted through SIM swapping attacks.
Who it helps: Anyone with online accounts. This protects you from credential theft and account takeovers.
Step 2: Update Devices and Remove Apps You Do Not Use
Outdated software is a common entry point for hackers.
- Turn on automatic updates for your operating system, browser, and apps.
- Delete apps you no longer use because they can still collect data in the background and may not receive security patches.
Who it helps: Everyone. This reduces your attack surface and limits unnecessary data collection.
Step 3: Tighten Browser Privacy and Reduce Tracking
Adjust your browser's privacy settings to block third-party cookies and tracking.
- In Chrome, go to Settings > Privacy and security > Third-party cookies and choose "Block third-party cookies."
- In Firefox, select "Strict" under Enhanced Tracking Protection.
- In Safari, enable "Prevent cross-site tracking."
- Install extensions like uBlock Origin or Privacy Badger for additional blocking.
Remember that third-party cookies aren't going away automatically in Chrome, so you need to manage this yourself.
Who it helps: Anyone who browses regularly. This limits how advertisers track you across the web.
Step 4: Audit Your Google Account Data
- Go to myactivity.google.com and review what Google has collected.
- Delete items you don't want stored and set auto-delete for 3, 18, or 36 months.
- Turn off Web & App Activity if you want Google to stop tracking entirely, but note that this disables personalized search results and recommendations.
- Use the "Results about you" feature to monitor when your personal information appears in search results.
- If you use other Google services heavily, repeat this process for YouTube History and Location History.
Who it helps: Google users who want control over their data. This reduces how much Google stores long-term.
Step 5: Clean Up Social Media And Public Profiles
- Review your privacy settings on Facebook, Instagram, Twitter, LinkedIn, and other platforms.
- Set your profile to private or friends-only, limit who can see your posts and photos, disable facial recognition if available, and turn off location tagging.
- Go through old posts and delete anything you wouldn't want a potential employer, family member, or stranger to see.
- Use the "View as" feature to see what your profile looks like to the public.
Who it helps: Social media users concerned about reputation and oversharing. This limits who can see your personal life.
Step 6: Restrict Location Tracking
Location data reveals where you live, work, shop, and spend time.
- On iPhone, go to Settings > Privacy & Security > Location Services and set most apps to "While Using the App" or "Never."
- On Android, go to Settings > Location > App permissions and do the same. Turn off location history in Google Maps (Settings > Maps history > Turn off).
- Disable location access entirely for apps that don't need it, like games, flashlight apps, or weather apps that can use your zip code instead.
Who it helps: Mobile users who want to prevent always-on tracking. This protects your movements and routines.
Step 7: Remove Your Information from Data Brokers
Data brokers sell your personal information to advertisers, employers, and anyone willing to pay.
- Start by opting out of the biggest brokers: Spokeo, Whitepages, BeenVerified, Intelius, PeopleFinder, and Radaris.
- Each site has its own opt-out process, usually buried in a privacy policy or help section.
- You'll need to submit your name, address, and sometimes additional verification.
- Repeat this process every six months because brokers refresh their databases regularly.
- If you're in California, the Delete Act (DROP) program lets you submit a single opt-out request to cover multiple brokers.
Who it helps: Anyone whose information appears on people-search sites. This makes you harder to find and reduces unsolicited contact.
You can DIY removal, but it is time-consuming. Paid services like DeleteMe, Incogni, or Privacy Bee charge a subscription fee (typically $100 to $200 per year) and handle opt-outs for you. They monitor brokers and resubmit requests as needed. If your time is limited or you're at higher risk (public figure, domestic violence survivor, law enforcement), paid services may be worth it.
Step 8: Secure Your Home Wi-Fi and Connected Devices
- Change default router passwords
- Use WPA2 or WPA3 encryption
- Update router firmware
Securing your network, devices, and accounts are core steps in protecting your privacy. Set a reminder to check in on them and change the passwords every couple of months.
Who it helps: Anyone running a home network with a Wi-Fi router or gateway.
Step 9: Use VPNs on Public Wi-Fi
Public Wi-Fi networks at coffee shops, airports, and hotels are often unencrypted, meaning anyone on the same network can potentially intercept your traffic. A VPN (virtual private network) encrypts your connection and hides your IP address. Use a reputable VPN like Mullvad, ProtonVPN, or IVPN when you're on public networks. Avoid free VPNs, which often sell your data to advertisers.
Who it helps: Travelers and remote workers. This protects your data when you're not on a trusted network.
Step 10: Review Smart Device Settings
Smart speakers, security cameras, and connected appliances collect audio, video, and usage data.
- Review the privacy settings for each device.
- Disable always-on listening if you don't need it, turn off cloud storage for camera footage, and delete old recordings regularly.
- Check whether your devices share data with third parties and opt out if possible.
Who it helps: Smart home users. This limits how much data your devices collect and share.
How to Remove Your Info from Data Brokers
Data broker removals are annoying, but they are one of the most meaningful ways to protect your online privacy because they reduce exposure beyond a single app or account.
Option A: DIY Opt-Outs
- Search your name and city and identify the major people-search listings (Whitepages, Spokeo, TruthFinder, Intelius, and BeenVerified)
- Find each site’s opt-out process by searching "[broker name] opt out," and look for links in their privacy policy or help section.
- Save confirmation emails or screenshots
- Re-check every few months
Be aware that some brokers have been reported to obscure opt-out pages from search engines, which makes the process harder than it should be.
Option B: Use A Removal Service
Companies like DeleteMe, Incogni, and Privacy Bee charge up to $200 per year and handle opt-outs continuously for you. They monitor brokers, resubmit requests, and send you reports on what's been removed. These are best for people who want ongoing protection without the hassle of doing it manually.
If You Live in California: DROP Changes the Game
California’s DROP (Data Broker Removal Portal) lets residents submit one request to over 500 registered data brokers. Brokers must start processing deletion requests beginning August 1, 2026.
What Digital Privacy Laws and Rights Apply to You?
Privacy laws in the U.S. vary by state, but several give you legal rights over your personal data. Here's what you can do under these laws.
Your Privacy Rights Checklist
If you live in a state with comprehensive privacy legislation, you may have the following rights:
- Right to access: Request a copy of the personal data a company has collected about you.
- Right to delete: Ask companies to delete your data, with some exceptions for legal or security reasons.
- Right to correct: Request corrections to inaccurate information.
- Right to opt out of sale or sharing: Tell companies not to sell or share your data with third parties.
- Right to limit use of sensitive data: Restrict how companies use sensitive categories like health data, biometrics, or precise location.
How Many States Have Privacy Laws?
As of January 2026, more than a dozen U.S. states have enacted comprehensive privacy laws, according to tracking by the International Association of Privacy Professionals (IAPP) and the National Conference of State Legislatures (NCSL). California led with the California Consumer Privacy Act (CCPA) in 2018 and strengthened it with the California Privacy Rights Act (CPRA) in 2020. Other states with active laws include Virginia, Colorado, Connecticut, Utah, Iowa, Indiana, Tennessee, Montana, Oregon, Texas, and Delaware. Florida and several others are expected to implement laws soon.
Each state's law has different thresholds, exemptions, and enforcement methods, so protections vary depending on where you live and which companies you interact with.
Global Privacy Control (GPC)
Global Privacy Control (GPC) is a browser signal that tells websites you want to opt out of data sales and sharing. You can enable it in browsers like Firefox, Brave, or DuckDuckGo, or as an extension in Chrome.
When you visit a website, GPC sends a signal indicating your preference, and companies legally required to honor it must comply. It's not foolproof (some sites ignore it), but it's a simple way to enforce your rights automatically.
Make Privacy A Habit: Your Monthly 10-Minute Check
You do not need a “perfect” privacy setup. You need a repeatable one. Set a recurring reminder to spend 10 minutes each month on these tasks:
- Review your Google My Activity and delete anything you don't want stored.
- Check that auto-delete is still enabled.
- Look at your app permissions on your phone and revoke access for apps that don't need location, camera, or microphone.
- Run a quick search for your name and address on a people-search site to see if new listings have appeared, and submit opt-outs if needed.
- Check your password manager to see if any passwords have been compromised in breaches and update them.
- Enable passkeys on any new accounts that support them.
These small, regular actions compound over time. Start with one step today, add another next week, and build from there.
Your privacy is worth protecting, and you have more control than you think.
FAQ
How Can I Protect My Privacy Online Quickly?
Start by locking down your accounts with unique passwords, two-factor authentication, and passkeys where available. Then update your phone and computer, review app permissions (especially location settings), tighten your browser privacy settings, and secure your home Wi-Fi. These quick steps cover the biggest everyday privacy risks without needing advanced tools.
How do I know if my data has been in a breach?
Use a service like Have I Been Pwned to check if your email address or phone number has appeared in any known breaches. Enter your email and the site will show which breaches had your data. If you find a match, change your password immediately on the affected site and enable multi-factor authentication.
What Does Google Know About Me, And Where Can I See It?
Google can collect information tied to your account and how you use its services, such as your search activity, YouTube watch history, location-related activity (like Maps Timeline), and interactions with ads. You can review and manage much of this data in your Google Account under My Activity, where you can search, filter by date or product, and delete items or time ranges, and set up auto-delete.
How Do I Delete My Google Search History (Or Set Auto-Delete)?
Go to myactivity.google.com, select "Delete activity by," choose "All time," and confirm. To prevent Google from collecting future data, turn off Web & App Activity in your account settings. Keep in mind this will disable personalized search results and recommendations.
Is incognito mode enough to stay private?
No. Incognito mode only prevents your browser from saving your history and cookies on your device. It doesn't hide your activity from your internet provider, employer, school, or the sites you visit. For better privacy, adjust your account settings, use tracking protection, and consider a VPN.
How Do I Remove My Personal Info from Google Search Results?
Use Google’s “Results about you” tool to find search results that show your personal contact details (like your phone number, home address, or email) and submit a removal request right from your Google Account. If the “Results about you” option is not available, you can also use Google’s personal information removal request form. Check out this resource from Google for more details about removing your personal info.
Removing a result from Google Search does not delete the information from the original website, so you may need to contact the site to have it taken down at the source.
Are Passkeys Better Than Passwords?
Yes, in most cases. Passkeys are generally better than passwords because they use public-key cryptography and are phishing-resistant by design, and they are unique to each site, so there is no reusable password for attackers to steal or reuse elsewhere. They are also easier to use (often a face scan, fingerprint, or device PIN) and are already being adopted by major platforms.